|
CMS released its annual proposed changes to the Physician Fee Schedule for 2022, which expands certain Medicare telehealth provisions and updates the payment rate for physician services.
Each year there are updates to the Physician Fee Schedule and the “Proposed Rules” enter into a comment period where providers and healthcare industry organizations weigh in on those proposed changes. This year they are as important as ever.
1 Comment
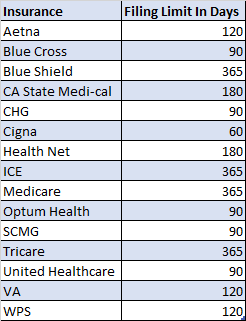
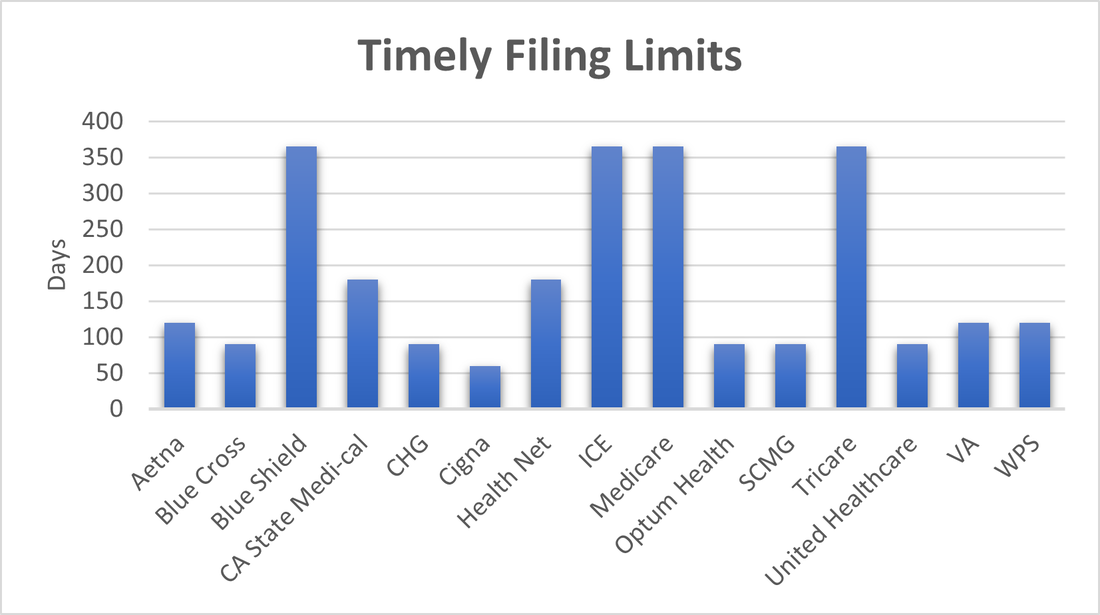
We are all familiar with insurance timely filing limits. Those deadlines listed in your provider contracts and manuals that state the amount of time after the date of service that you have to submit your claims to the insurance. Anything received after this time frame will automatically be denied for past timely filing limits and you will not be paid for these services. We wanted to review some of the most common filing limits that we have recently seen within our providers contracts and in published insurance manuals. These show the importance of turning in your billing timely and asking patients at each visit if their insurance has recently changed.
“While 62% of breaches in 2020 were related to hacking, healthcare insiders themselves accounted for 1 in every 5 breaches.”
We hear about healthcare breaches almost every day lately. Insurance companies that had a breech and had millions of records accessed, healthcare systems that were subject to hackers and even providers themselves losing track of PHI. Even if you do not host your patient health information directly, you need to always be aware and continue to monitor the systems you have in place, to make sure the information is being guarded at all times. Who is in charge of your internal passwords, setting up new users, terminating employees that have left? When did you last do a Security Risk Assessment? These are questions that you should be reviewing at least quarterly and documenting the outcomes.  We’ve all heard about 2-step/factor verification methods for some time. It helps protect against fraud by requiring an additional layer of authentication such as text message or email in order to access or change your account information. As this practice becomes more widespread, how many of us have taken the time to set up this security protocol on each site that offers it? Who wants to look at yet another device/email/text message just to access one of their accounts? Now imagine that you are logged into your online Quickbooks account one day… You can see the details of your account on your computer screen as you organize papers on your desk. Out of the corner of your eye, you notice your mouse moving across your screen… WITHOUT YOU TOUCHING IT! As you watch in horror, the mouse adds a vendor. A payee you have never heard before. Your phantom mouse then begins issuing a check to this mystery vendor-from YOUR checking account. This may sound far fetched, but it recently happened to one of our clients. Although they were able to get their money returned, we have now learned that it could have been prevented by utilizing Quickbooks’ 2-step verification option. We highly recommend utilizing 2-step verification methods on any websites that offer them. This added layer of security is vital to keeping your information private and secure. To make the process a little easier, some sites offer an option to “remember your device”. This will eliminate the need to re-verify your device on the next log in. So next time you are asked if you would like to set up a 2-step verification process, ask yourself, how much money could those 5 minutes of your time really be worth? |
Categories
All
Archives
January 2023
|
|
© COPYRIGHT 2021. ALL RIGHTS RESERVED.
Privacy Policy Terms of Service |